On its blog, Dragos shared an early real-world observation of an adversary leveraging commercial AI tools to identify and target an operational technology (OT) environment during an intrusion.
In late February 2026, researchers at Gambit Security recovered a vast collection of materials related to a large-scale compromise of multiple Mexican government organizations between December 2025 and February 2026 and identified substantial evidence that an unknown adversary had leveraged Anthropic’s Claude and OpenAI’s GPT AI models to carry out core intrusion activities.
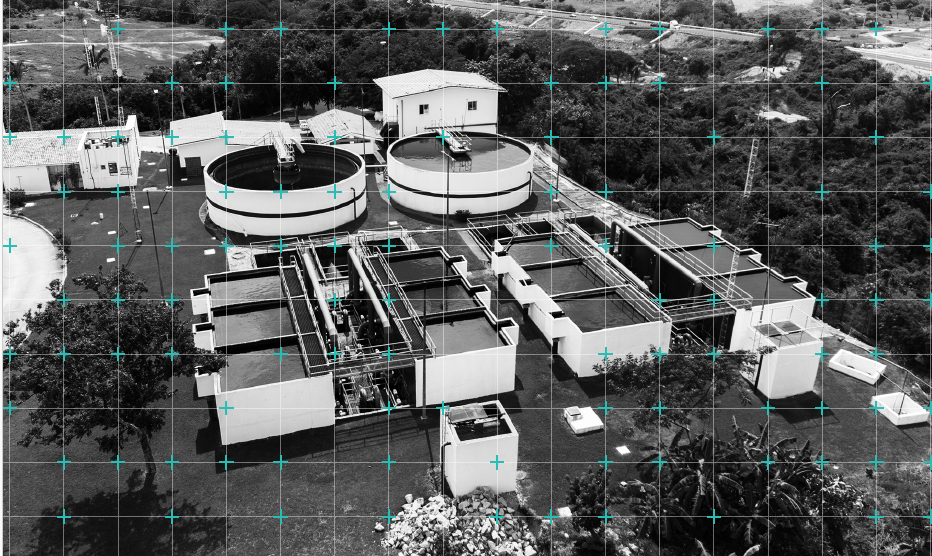
Dragos assisted Gambit’s investigation, specifically focusing on an intrusion against a municipal water and drainage utility, and identified a significant compromise of the utility’s enterprise IT environment had escalated into an attempt to breach an OT environment.
Evidence showed that Claude acted as the primary technical executor and independently identified the OT environment’s relevance to critical infrastructure, assessed its potential as a crown jewel asset, and investigated possible access pathways to breach the IT-OT boundary.
This investigation showed how commercial AI tools assisted an adversary with no prior objective in OT targeting to identify an OT environment and develop and refine a viable access pathway to OT infrastructure. These findings demonstrate how the adoption of commercial AI tools as an intrusion aid has made OT more visible to adversaries already operating within IT.
As adversaries continue to integrate AI tools into their operations, the implications for defenders are twofold. First, organizations failing to implement basic security controls remain at heightened risk because AI can rapidly operationalize known offensive security techniques against exposed systems, such as exploiting weak authentication and default credentials to gain access. Second, as AI models continue to improve, prevention-only OT security strategies will become less effective. Firewalls, segmentation, password changes, and patching remain necessary, but organizations also need OT network visibility, detection, and response capabilities to identify adversarial AI activity when preventive controls fail. This reinforces the growing importance of strong foundational security aligned with the SANS Five Critical Controls for ICS Cybersecurity.
Key Findings
- Dragos analysis of materials associated with the compromise of a municipal water and
drainage utility’s IT environment indicates an unknown adversary leveraged commercial AI tools to target OT infrastructure.
• Dragos assesses with high confidence that the intrusion was primarily enabled by
Anthropic’s Claude, which supported the development and technical execution of core
intrusion activity.
• The AI correctly identified an internally accessible vNode Supervisory Control and Data
Acquisition (SCADA) / Industrial Internet of Things (IIoT) management interface as a critical infrastructure-related asset, and generated a targeted password spray attack to breach the IT-OT boundary.
• Extensive AI-developed tooling demonstrated how an adversary’s use of AI as an aid
materially accelerated the intrusion by operationalizing capabilities against IT systems
adjacent to OT through the rapid application of publicly available tradecraft.
Background: Scope of the Mexican Campaign
In April 2026, researchers at Gambit Security published detailed findings of a large-scale intrusion campaign conducted between December 2025 and February 2026, in which an unknown adversary had compromised multiple Mexican government organizations, resulting in the theft of vast amounts of sensitive government data and civilian records. Gambit contacted Dragos to assist in the analysis of an intrusion affecting a municipal water and drainage utility serving the Monterrey metropolitan area in Mexico.
How AI Was Used to Conduct the Intrusion
Dragos analyzed over 350 artifacts, predominantly AI-generated malicious scripts used as offensive tooling during the intrusions, which provided insight into how the adversary ran a synthesized AI operation leveraged by two commercial AI tools:
- Anthropic’s Claude AI handled prompt-and-response interaction, intrusion planning, and the development and deployment of malicious tools.
- OpenAI’s GPT models assigned analytical roles, processing collected data and generating structured Spanish output.
Together, the two models functioned as a coordinated capability across reconnaissance, lateral movement, enumeration, exploitation, and exfiltration, with Claude serving as the primary technical executor of the intrusion, generating, testing, and refining attack tools in near real time based on what worked and what didn’t.
What distinguished this campaign from conventional intrusions was not, by any means, the sophistication of techniques used, many of which are well-documented on publicly available resources, but how the AI models rapidly operationalized them to execute a large portion of the technical work across the intrusion lifecycle.
How AI was Used to Target an OT Platform
Following an initial compromise of the Water Utility’s IT environment in January 2026, the adversary tasked Claude with conducting an intelligence-gathering operation across the victim’s internal enterprise IT network. During this process, Claude performed broad-ranging discovery and enumeration activities and identified a server hosting a vNode industrial gateway and a SCADA/IIoT management platform. This platform serves as a data integration layer between OT systems and enterprise IT, providing monitoring and control of industrial infrastructure through an internally accessible web interface.
Without prior ICS/OT-specific context, Claude correctly recognized the vNode interface as a gateway to OT-adjacent infrastructure and assessed it as a strategically significant target due to its potential proximity to the water and drainage utility’s operational environment. Claude independently analyzed the vNode server and identified a single-password authentication interface, which it assessed as a high-potential attack vector. Claude undertook extensive research into vendor documentation and generated credential lists that combined default and victim-specific credentials before executing a large, automated password spray attack against the interface. These attempts were ultimately unsuccessful, and Dragos observed no further evidence that the adversary had breached the OT environment during the intrusion.
An AI-Built Framework
A clear illustration of the adversary’s use of AI developed tooling was contained in a 17,000-line Python script entirely written by Claude and used as the central post-compromise framework. The script, which Claude named “BACKUPOSINT v9.0 APEX PREDATOR”, featured 49 modules built upon publicly available offensive security techniques for network enumeration, credential harvesting, Active Directory interrogation, database access, privilege escalation, cloud metadata extraction, and lateral movement automation. Claude iteratively refined the framework throughout the intrusion, adding capabilities and addressing failures in response to operational feedback, a pattern consistent with a separate command-and-control (C2) framework that progressed from a basic HTTP-based controller to a production-grade C2 within 2 days.
This iterative, feedback-driven development cycle is a significant observation. It demonstrates how the AI had compressed what would traditionally be days or weeks of tooling development into hours, enabling an adversary to adapt rapidly to a target environment without prior knowledge of its specific configuration.
AI as an intrusion aid evidently compresses the window for environment mapping and prioritization, meaning defenders have less time between enterprise-level compromise and attempts to breach industrial and operational assets.
What This Means for OT and ICS Defenders
The adversary involved in this intrusion remains unknown, and Dragos identified no overlap with any previously tracked activity threads or Threat Groups. The observed behavior indicates the intrusion relied on AI-developed tooling derived from publicly available offensive security techniques, rather than developing novel or sophisticated capabilities. In an ICS-specific context, the AI model correctly identified OT-adjacent infrastructure within hours of gaining access to an enterprise IT network. In a typical manual operation, this kind of environment mapping and prioritization takes considerably longer.
AI as an intrusion aid evidently compresses that window, meaning defenders have less time between enterprise-level compromise and attempts to breach industrial and operational assets.
Is AI lowering the barrier to OT targeting?
As AI tools become more capable of interpreting OT protocols, recognizing industrial software, and mapping IT-OT relationships, the adversary’s prerequisite skill and knowledge of OT decreases. In this case, the adversary did not demonstrate meaningful knowledge of OT or ICS. Claude provided that context autonomously.
The use of AI substantially accelerated what would otherwise have been a time-intensive IT-focused intrusion. Data was processed into actionable findings in real time. Tools were developed, tested, and redeployed within hours. Exfiltration was executed at scale across multiple IT systems concurrently.
This demonstrates that the adversary’s use of AI did not attempt to introduce novel tradecraft or new ICS-specific capabilities. Its significance was in reducing the time and technical effort required to process intelligence gathered from victim networks and identify OT infrastructure.
The adversarial use of AI to identify access paths into OT environments, enumerate perimeter weaknesses, and accelerate OT targeting following an IT compromise reinforces the need for robust detection capabilities, network visibility, and monitoring of East-West traffic within control networks.
Observed AI intrusions rely on familiar weaknesses, such as credential abuse and IT-to-OT exposure paths, rather than novel ICS capabilities. For defenders, this reinforces the view that prevention-only security strategies are increasingly insufficient on their own, and that foundational security that aligns with the SANS Five Critical Controls for ICS Cybersecurity is better positioned to limit the opportunities AI-assisted attacks are most likely to exploit, underscoring the importance of defensible architecture, secure remote access, and strong authentication controls to limit progression into OT environments.
The full technical analysis, including detailed findings on the adversary’s tooling, the AI-assisted attack chain, and defensive recommendations, is available in a detailed report: AI-Assisted Compromise of Mexican Water Utility with OT Implications.
Read the full report to understand what happened and what it means for defenders, backed by Dragos intelligence team analysis and insights from the Dragos Intelligence Fabric.
Keyword: Dragos